MSEE Thesis Defense
Reliability of Structural Equation Modeling in Examining Resting State Motor Network in Healthy Subjects
Tejaswini Kavallappa
3pm Monday, 16 May 2011, ITE 325
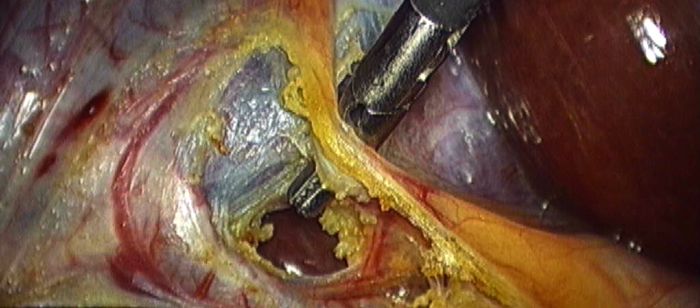
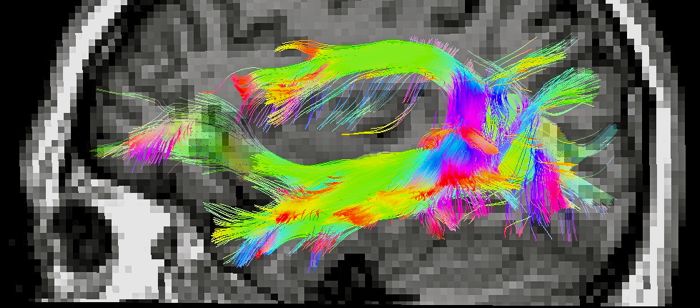
Resting state connectivity studies are of growing significance and interest in the current neuroimaging literature due to their potential in explaining various underlying brain mechanisms and, therefore, their utility in clinical applications. While functional connectivity has been extensively examined in the human brain, effective connectivity is a burgeoning field in functional neuroimaging studies, and there is an increased interest in quantifying effective connectivity that takes into account the directional influences of various brain regions active in a particular functional network. Studies have shown the presence of multiple functional networks in the resting state, which have been shown to be consistent across subjects and between sessions. However, this is not the case with resting state effective connectivity.
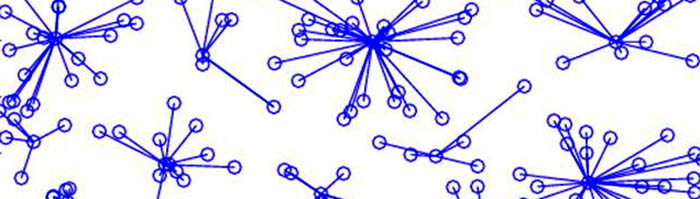
In this thesis we evaluate effective connectivity of the resting state motor network in normal subjects using structural equation modeling (SEM), a linear statistical analysis method. It has been shown that signals related to cardiac pulsatality and respiration effects can confound functional MRI results. Thus, we have investigated the effect of various filtering strategies on the reliability of effective connectivity measurements. Our thesis examined the effect of four methods of physiological filtering of resting state data:
- preprocessed data without any filtering,
- removal of prospectively recorded cardiac and respiratory fluctuations using RETROICOR,
- removal of global average signal from all the brain voxels time series,
- regressing out average signal of the white matter (WM) and cerebrospinal fluid (CSF), and
- temporal filtering to remove frequencies pertinent to cardiac and respiratory sources.
The resulting effect of each of these methods on the estimation of resting state motor network effective connectivity was examined in this thesis.
Committee:
- Dr. Joel M. Morris (chair)
- Dr. Rao P. Gullapalli (co-advisor)
- Dr. Tulay Adali
- Dr. Alan B. McMillan